🗣️ Overview # This research topic proposes a cross-architecture software birthmarks that targets the real-world executables such as Linux ELF, Windows PE, and macOS Mach-O. The birthmarks are extracted from the intermediate representation of the executables throughGhidra’s p-code.
📚 Publications # 🔎 Related Research Topics # Concept of Software Birthmarks Fast comparisons of the birthmarks 🤝 Collaborators # Y. Kanzaki@Kumamoto National College of Technology
Introduces my research works. The main research areas are: empirical software engineering, software security (software theft detection, software obfuscation), and program education.
The software birthmark toolkit for LLVM IR.
Java birthmark toolkit, detecting the software theft by native characteristics of the programs.
Java Birthmarking Toolkit. It instead of using tamada/pochi.
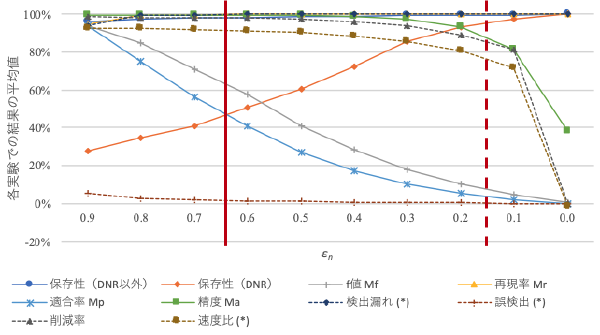
:speaking_head: Overview # The software birthmarks were proposed for detecting the software theft from a large number of suspected programs. The birthmark is a technique to compare the extracted characteristics as the software birthmarks, and compute similarities between two birthmarks. The conventional birthmarks require a much time by increasing the target programs for comparison. Therefore, it is the bottleneck of the conventional birthmarking technique. In this paper, we propose a method for reducing total processing time by introducing the narrowing phase between conventional extracting and comparison phases. The narrowing phase employs the fast but rough comparison algorithm in order to eliminate unrelated programs.